Anomaly Detection using Extreme Value Theory
Extreme Value Theory (EVT) is used to model extreme events like 100-year old floods. Detecting anomalies using EVT reduces falsely identifying observations as anomalies. This set of papers are methodological and applied contributions using EVT to detect anomalies. The applications mostly come from cyber security.
Leave-one-out kernel density estimates for outlier detection
Authors: Sevvandi Kandanaarachchi, Rob J. HyndmanVenue: Journal of Computational and Graphical Statistics, 2021
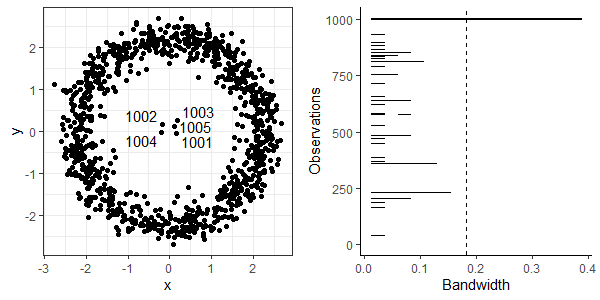
TLDR: Persistent homology-based bandwidths help to find anomalies in data using Extreme Value Theory.
lookout: Leave-one-out kernel density estimates for outlier detection
When lookout sees crackle: Anomaly detection via kernel density estimation
Authors: Rob J. Hyndman, Sevvandi Kandanaarachchi, Katharine TurnerTLDR: An updated version of lookout algorithm using theoretical underpinnings of persistent homology.
When lookout sees crackle: Anomaly detection via kernel density estimation
We do theoretical proofs of bandwidth convergence and update the lookout algorithm accordingly. In addition, we scale the data usinga robust multivariate scaling. These updates make the lookout algorithm more robust and efficient.
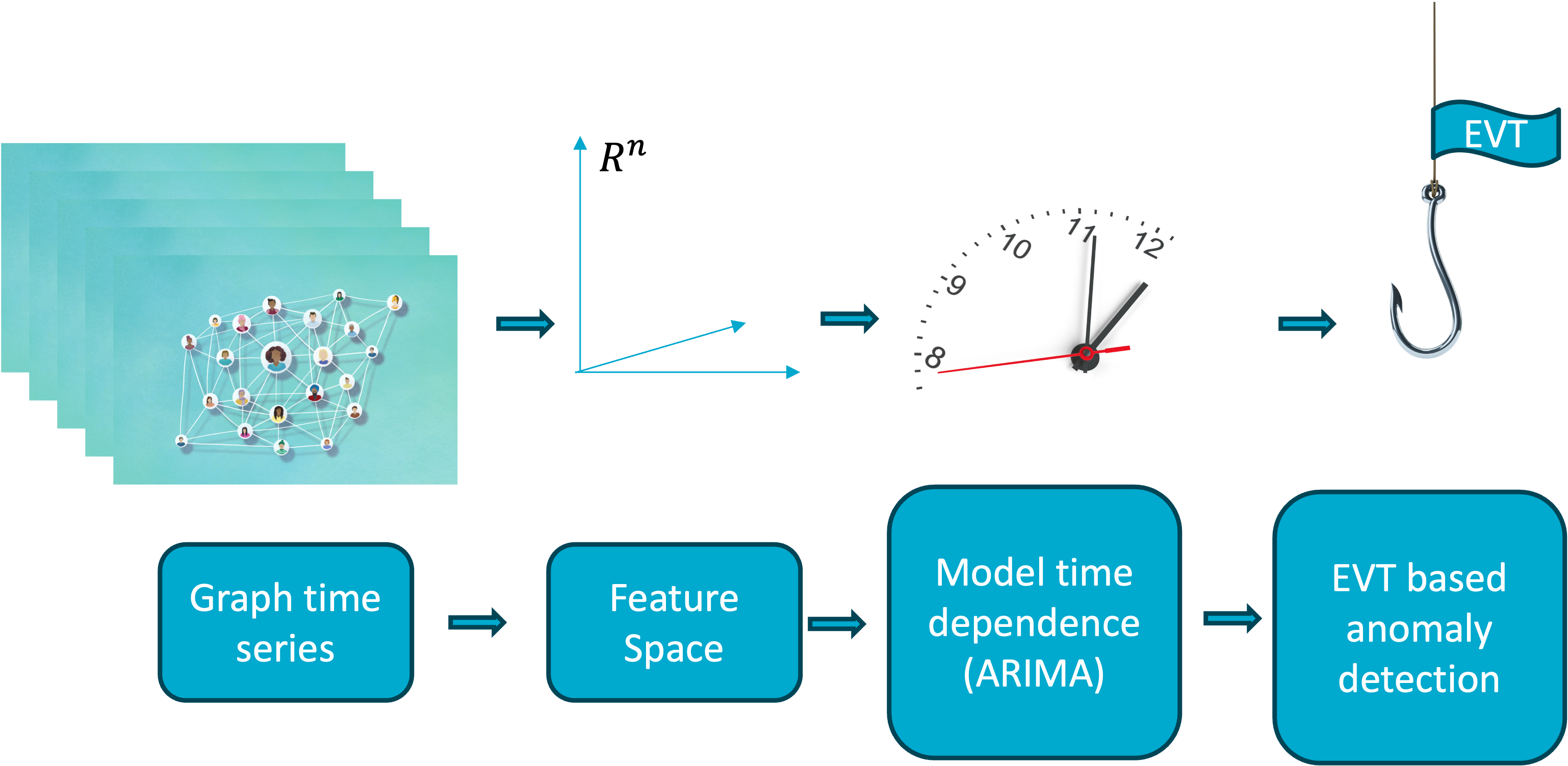
Extreme value modelling of feature fesiduals for anomaly detection in dynamic graphs
Authors: Sevvandi Kandanaarachchi, Rob J. Hyndman, Conrad SandersonVenue: 11th International Conference on Soft Computing & Machine Intelligence (ISCMI), 2024
TLDR: Model the network’s time dynamics first, then use extreme value theory to flag true anomalies reducing false positives.
Extreme value modelling of feature fesiduals for anomaly detection in dynamic graphs
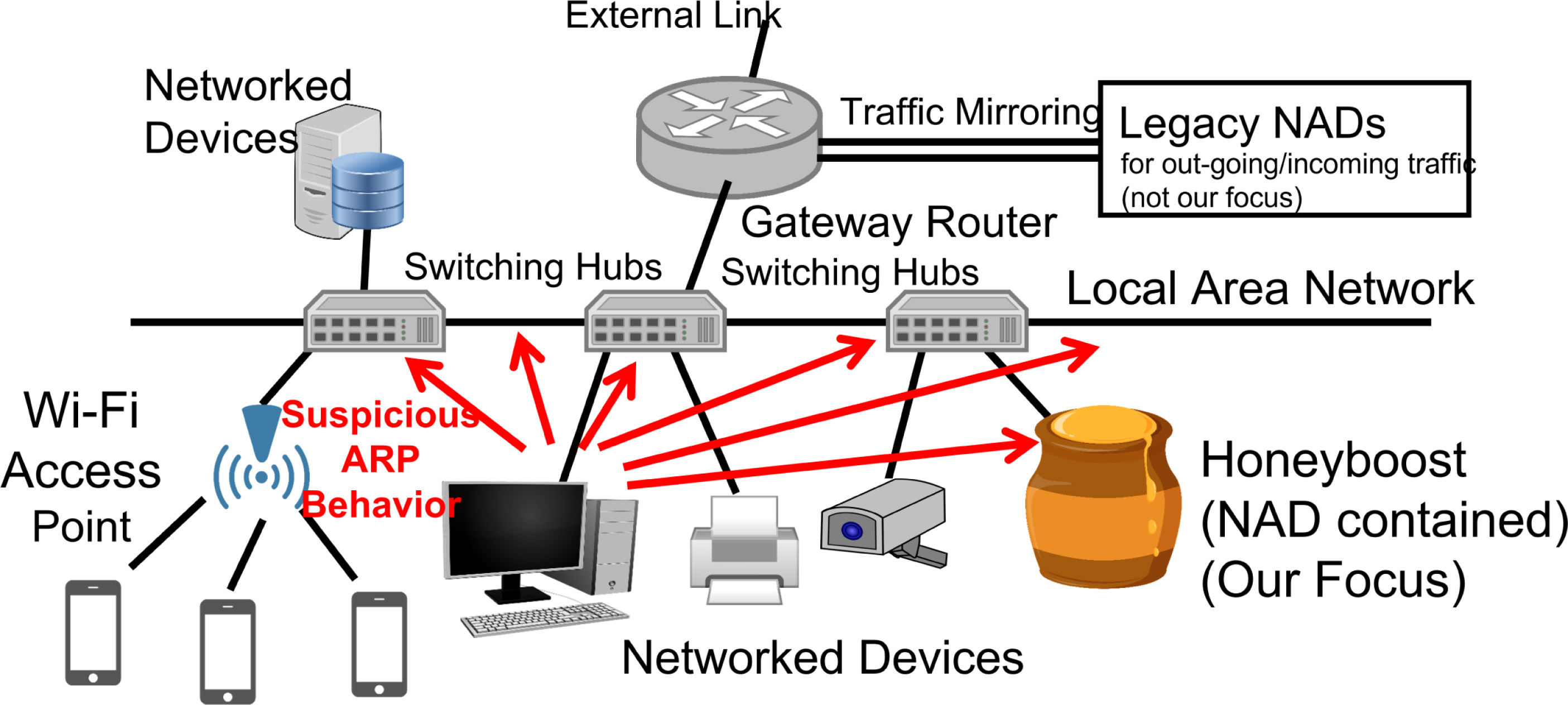
Honeyboost: Boosting honeypot performance with data fusion and anomaly detection
Authors: Sevvandi Kandanaarachchi, Hideya Ochiai, Asha RaoVenue: Expert Systems with Applications, 2022
TLDR: Honeyboost detects insider threats early by monitoring internal network traffic with low false positives, combining anomaly detection and honeypots inside the LAN rather than at the network perimeter.
Honeyboost: Boosting honeypot performance with data fusion and anomaly detection
Detection of anomalous network nodes via hierarchical prediction and Extreme Value Theory
Authors: Sevvandi Kandanaarachchi, Mahdi Abolghasemi, Hideya Ochiai, Asha Rao, Conrad SandersonTLDR: Model ARP behaviour over time and use extreme value theory to spot truly abnormal activity, reducing false positives when detecting compromised devices in industrial networks.
Detection of anomalous network nodes via hierarchical prediction and Extreme Value Theory
As cyber‑attacks on industrial networks grow more sophisticated, traditional signature‑based defences are becoming less effective—especially once malware is already inside the network. Infected devices often reveal themselves through unusual patterns in Address Resolution Protocol (ARP) traffic. This work introduces a two‑stage approach that first models normal ARP behaviour using time‑series prediction, then applies Extreme Value Theory to reliably flag truly abnormal activity. By accounting for the heavy‑tailed nature of network traffic, the method significantly reduces false alarms, helping address alert fatigue while enabling more reliable detection of compromised devices.